
-
 English
English
-
 Español
Español
-
 Portugues
Portugues
-
 Pусский
Pусский
-
 Français
Français
-
 Deutsch
Deutsch
-
 日本語
日本語
-
 한국어
한국어
-
 العربية
العربية
-
 Italiano
Italiano
-
 Nederlands
Nederlands
-
 Ελληνικά
Ελληνικά
-
 Svenska
Svenska
-
 Polski
Polski
-
 ไทย
ไทย
-
 Türk dili
Türk dili
-
 हिन्दी
हिन्दी
-
 Indonesia
Indonesia
-
 Melayu
Melayu
-
 Tiếng Việt
Tiếng Việt
-
 中文
中文
-
 dansk
dansk
-
 Magyar
Magyar
-
 қазақ
қазақ
-
 বাংলা
বাংলা
-
 עִברִית
עִברִית
-
 čeština
čeština
-
 Soomaali
Soomaali
-
 မြန်မာ
မြန်မာ
-
 فارسی
فارسی
-
 українська
українська
-
 norsk
norsk
-
 Gaeilge
Gaeilge
-
 беларускі
беларускі
-
 Română
Română
-
 ພາສາລາວ
ພາສາລາວ
-
 Filipino
Filipino
-
 lietuvių
lietuvių
-
 Cymraeg
Cymraeg
-
 македонски
македонски
-
 Suomalainen
Suomalainen
-
 slovenský
slovenský
-
 o'zbek
o'zbek
-
 اردو
اردو
-
 հայերեն
հայերեն
-
 Igbo
Igbo
-
 български
български
-
 سنڌي
سنڌي
-
 Shona
Shona
-
 සිංහල
සිංහල
-
 Hrvatski
Hrvatski
-
 íslenskur
íslenskur
-
 galego
galego
-
 català
català
-
 Zulu South Africa
Zulu South Africa
-
 Afrikaans isiXhosa
Afrikaans isiXhosa
-
 ಕನ್ನಡ
ಕನ್ನಡ
-
 lëtzebuergesch
lëtzebuergesch
-
 Indonésia Sunda
Indonésia Sunda
-
 basa jawa
basa jawa
-
 ગુજરાતી
ગુજરાતી
-
 Кыргызча
Кыргызча
-
 тоҷикӣ
тоҷикӣ
-
 Србија
Србија
-
 Twi
Twi
-
 Hawaii
Hawaii
-
 Cebu
Cebu
-
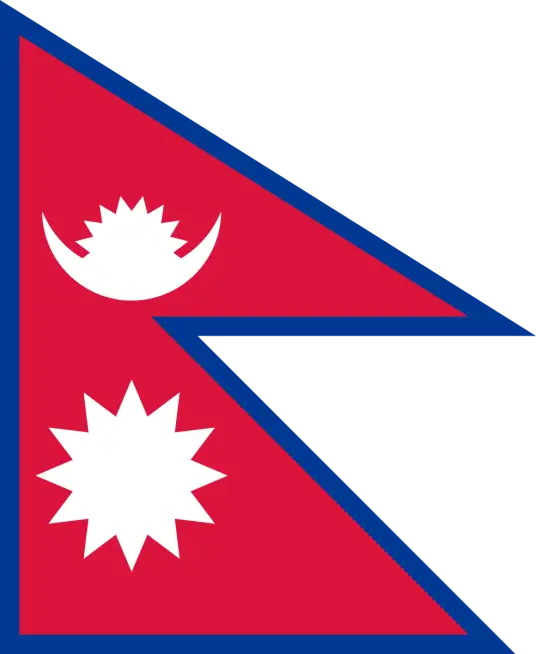
 नेपाल
नेपाल
-
 euskara
euskara
-
 Kurdî
Kurdî
-
 frissi
frissi
-
 יידיש
יידיש
-
 latvija
latvija
-
 slovenija
slovenija
-
 kiswahili
kiswahili
-
 ਪੰਜਾਬ
ਪੰਜਾਬ
-
 پښتو
پښتو
-
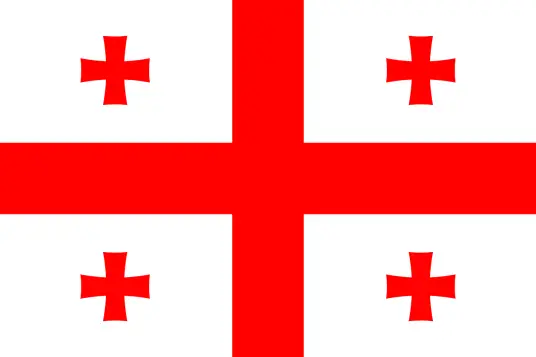
 საქართველოს
საქართველოს
-
 hua moni
hua moni
-
 bosna
bosna
-
 తెలుగు
తెలుగు
-
 தமிழ்
தமிழ்
-
 Kreyòl ayisyen
Kreyòl ayisyen
-
 Eesti
Eesti
-
 Corsica
Corsica
-
 Yoruba
Yoruba
-
 Gàidhlig na h-Alba
Gàidhlig na h-Alba
-
 Samoa
Samoa
-
 Монгол
Монгол
-
 Hausa
Hausa
-
 Azərbaycan
Azərbaycan
-
 አማራ
አማራ
-
 Shqipëria
Shqipëria
-
 Malagasy
Malagasy
-
 मराठी
मराठी
-
 മലയാളം
മലയാളം
-
 Malta
Malta
-
 ខ្មែរ
ខ្មែរ
-
 Chicheva
Chicheva
-
 中文(繁体)
中文(繁体)
-
 ଓଡିଆ
ଓଡିଆ
-
 Setswana
Setswana
-
 Afrikaans
Afrikaans
-
 Aymara
Aymara
-
 Башҡорт
Башҡорт
-
 Türkmenler
Türkmenler
-
 ትግሪኛ
ትግሪኛ
-
 Afaan Oromoo
Afaan Oromoo
-
 অসমীয়া
অসমীয়া
-
 Kinyarwanda
Kinyarwanda
-
 Ilocano
Ilocano
-
 Wolof
Wolof
-
 अवधी
अवधी
-
 Oluganda
Oluganda
-
 Bikol
Bikol
-
 Fulɓe
Fulɓe
-
 Kikongo
Kikongo
-
 Sango
Sango
-
 ދިވެހި
ދިވެހި
-
 Lingala
Lingala
-
 मैथिली
मैथिली
-
 Tsonga
Tsonga
-
 ꯃꯦꯏ ꯊꯥꯏ꯫
ꯃꯦꯏ ꯊꯥꯏ꯫
-
 brezhoneg
brezhoneg
-
 Furlan
Furlan
-
 नेवा
नेवा
-
 རྫོང་ཁ
རྫོང་ཁ
-
 Santali
Santali
-
 Аҧсуа
Аҧсуа
-
 Нохчийн
Нохчийн
-
 Чӑваш
Чӑваш
-
 Татар
Татар
-
 Batak Karo
Batak Karo
-
 دری
دری
-
 Diura
Diura
-
 Fengyu
Fengyu
-
 Eʋegbe
Eʋegbe
-
 Iban
Iban
-
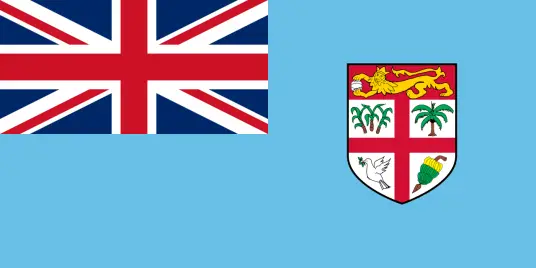 Fiji
Fiji
-
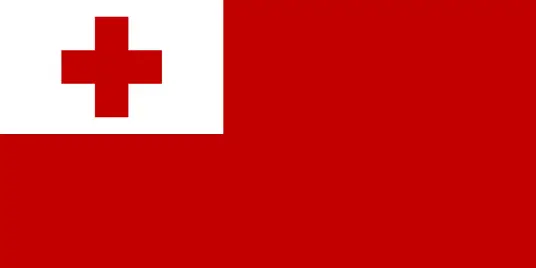 Tonga
Tonga
-
 Inuktitut
Inuktitut
-
 Nahuatl
Nahuatl
-
 maaya yucatec
maaya yucatec
-
 Runasimi
Runasimi
-
 guarani
guarani
-
 Acholi
Acholi
-
 Dinka
Dinka
-
 Luo
Luo
-
 Lundi
Lundi
-
 isiNdebele
isiNdebele
-
 Tshivenḓa
Tshivenḓa
-
 Sesotho sa Leboa
Sesotho sa Leboa
-
 Sesotho sa Borwa
Sesotho sa Borwa
-
 Ndumbe
Ndumbe
-
 Papuan Pidgin
Papuan Pidgin
-
 Rromani ćhib
Rromani ćhib
-
 Thok Nath
Thok Nath












 silki
silki